Compare IT Support Packages for Aberdeen Businesses
Review the IT support packages Aberdeen businesses rely on for complete technical ownership. We offer total transparency on what is included, what is optional, and exactly how we protect your operations. No hidden fees, just expert management.
Compare Our IT Support Packages
Pricing is available on request. Costs vary by the number of users, devices and the overall setup of your IT environment.
| Service | Professional | Advanced | Enterprise |
|---|---|---|---|
|
Security by Default
Security by Default removes the burden of deciding when security should be applied. Instead of relying on individual judgement, temporary fixes, or optional controls, protection is established as a fixed operating position from the start. This prevents security from being weakened under pressure, overlooked during change, or introduced only after issues appear. The result is a more stable environment where risks are addressed deliberately rather than reactively.
|
This service is included within the selected package and forms part of the standard service coverage provided for this tier. It is delivered as part of the package without any additional licensing or monthly cost. | This service is included within the selected package and forms part of the standard service coverage provided for this tier. It is delivered as part of the package without any additional licensing or monthly cost. | This service is included within the selected package and forms part of the standard service coverage provided for this tier. It is delivered as part of the package without any additional licensing or monthly cost. |
|
Endpoint Management
We place a 24/7 management agent on every laptop and desktop to monitor performance and fix issues automatically. This ensures your computers run smoothly without your staff needing to call for help. We actively monitor:
Many providers do not have this full capability, or they disable these detailed alerts because it creates too much work for them. We keep them active to catch faults early, repairing your devices proactively rather than waiting for them to break. |
This service is included within the selected package and forms part of the standard service coverage provided for this tier. It is delivered as part of the package without any additional licensing or monthly cost. | This service is included within the selected package and forms part of the standard service coverage provided for this tier. It is delivered as part of the package without any additional licensing or monthly cost. | This service is included within the selected package and forms part of the standard service coverage provided for this tier. It is delivered as part of the package without any additional licensing or monthly cost. |
|
Patch Management
Patch Management ensures your systems remain secure and up to date without relying on manual updates or user intervention. By applying updates consistently across operating systems and applications, it reduces exposure to known vulnerabilities and helps maintain a stable, protected environment. Updates are managed in a controlled and predictable way, minimising disruption while maintaining strong security coverage as your systems evolve.
|
This service is included within the selected package and forms part of the standard service coverage provided for this tier. It is delivered as part of the package without any additional licensing or monthly cost. | This service is included within the selected package and forms part of the standard service coverage provided for this tier. It is delivered as part of the package without any additional licensing or monthly cost. | This service is included within the selected package and forms part of the standard service coverage provided for this tier. It is delivered as part of the package without any additional licensing or monthly cost. |
|
Endpoint Protection
Endpoint Protection secures your laptops and desktops by blocking malicious activity before it can affect your business. It reduces the risk of malware, ransomware, and credential theft while maintaining a stable and controlled user environment.
Protection levels can be adjusted independently, allowing you to strengthen device security without changing your overall service package. |
This service is included within the selected package and forms part of the standard service coverage provided for this tier. It is delivered as part of the package without any additional licensing or monthly cost. | Tier 2 (Advanced): Includes Tier 1, adding reputation filters and strict device policies to block suspicious domains and unknown risks. | This service is included within the selected package and forms part of the standard service coverage provided for this tier. It is delivered as part of the package without any additional licensing or monthly cost. |
|
Email Signature Management
Email Signature Management gives you full control over how your business is presented in every email. It ensures consistent branding, accurate company details, and professional formatting across all users without relying on individual setup or manual updates.
Included within your IT support package, delivering controlled branding and consistent communication without additional management effort or cost. |
This service is included within the selected package and forms part of the standard service coverage provided for this tier. It is delivered as part of the package without any additional licensing or monthly cost. | This service is included within the selected package and forms part of the standard service coverage provided for this tier. It is delivered as part of the package without any additional licensing or monthly cost. | This service is included within the selected package and forms part of the standard service coverage provided for this tier. It is delivered as part of the package without any additional licensing or monthly cost. |
|
Microsoft 365 Management
Microsoft 365 Management ensures your users, licences, and systems are handled efficiently without additional setup or change-related charges. From onboarding new staff to managing access and configurations, everything is delivered as part of your ongoing service.
All administration is included within your IT support package, providing predictable costs and removing the need for separate project-based charges. |
Included in all support packages (Standard, Advanced, and Pro) at no extra charge. | ||
|
Website Security
Website Security reduces the risk of compromise by protecting your site from common attacks, malware, and unauthorised access. It helps maintain trust, prevent disruption, and ensure your website remains stable and secure.
Delivered as a managed service with continuous oversight, providing visibility, accountability, and reduced reliance on reactive fixes. |
This service is available as an optional add-on and can be enabled if required. Add-ons are typically billed on a monthly or annual basis and can be adjusted as your organisation’s requirements evolve. | This service is available as an optional add-on and can be enabled if required. Add-ons are typically billed on a monthly or annual basis and can be adjusted as your organisation’s requirements evolve. | This service is included within the selected package and forms part of the standard service coverage provided for this tier. It is delivered as part of the package without any additional licensing or monthly cost. |
|
Website Hosting
Imagine investing in your website, then finding it blocked because of activity you did not cause. On low-cost shared hosting, your site can share a public IP address with hundreds or thousands of unrelated websites. If another site on that IP is associated with spam, phishing, malware or adult content, reputation feeds can flag the server and legitimate businesses can be caught in the fallout. We reduce that exposure with business-grade, managed website hosting designed for stability and clean infrastructure.
Under our Tier 1 managed model, all technical work is included. We handle migration, DNS routing and routine updates. You only pay the direct third-party costs for hosting, domains and SSL certificates. |
Fully managed across all packages. External licensing, domains, and hosting are supplied at cost. | Fully managed across all packages. External licensing, domains, and hosting are supplied at cost. | Fully managed across all packages. External licensing, domains, and hosting are supplied at cost. |
| Ready to get started? | Get a quote | Get a quote | Get a quote |
How Our IT Support Packages Aberdeen Protect Your Business
Structured and accountable by design
Each package is engineered with defined security controls, documented standards, and measurable oversight. You are not buying reactive support. You are implementing a structured operating model for your IT environment.
Every action is traceable, every configuration is intentional, and every change is governed. This ensures consistency, auditability, and long-term stability rather than short-term fixes.
Audit-ready and compliance-aligned
Your environment is maintained against defined security baselines, configuration standards, and documented controls. This provides clear technical evidence for internal reviews, external audits, and regulatory requirements where applicable.
We focus on operational discipline, not paperwork. Systems remain controlled, monitored, and aligned so you are prepared when verification, inspection, or compliance assessment is required.
How most cyber incidents actually begin
An employee receives what appears to be a legitimate Microsoft request to reset their password. The page looks genuine. Credentials are entered. Within minutes, the mailbox is compromised.
From that single entry point, attackers can read confidential emails, impersonate staff, access internal files, move across systems, and deploy ransomware or extract sensitive data.
Most incidents do not begin with sophisticated hacking. They begin with trust, weak controls, and lack of visibility. The difference between packages is how early threats are detected, contained, and evidenced.
What your IT support package protects you from
Professional Package
The Professional package delivers professionally managed IT with defined security controls, structured monitoring, and clear system visibility from day one. It establishes a stable, well-governed operating baseline without unnecessary complexity.
Professional is not a reduced service. It is a complete operating level suited to organisations with typical commercial risk. Advanced and Enterprise introduce deeper security oversight, expanded reporting, and stronger governance where exposure or regulatory pressure is higher. Packages remain flexible and can be formally adjusted, with additional services added where operational requirements evolve.
Advanced Package
The Advanced package builds on the Professional operating baseline with stronger security controls, enhanced monitoring, and structured reporting. It improves visibility, reduces user-driven risk, and introduces deeper operational oversight across endpoints and Microsoft 365.
This level is suited to organisations that require tighter operational control, regular security insight, and clearer management reporting without moving into full regulatory or high-assurance environments. As with all packages, the scope can be formally adjusted and additional services can be added where risk, scale, or operational needs change.
Enterprise Package
The Enterprise package delivers the highest level of security oversight, monitoring depth, and operational governance across your IT environment. It introduces advanced detection capability, deeper auditing, and structured review to ensure risks are identified, contained, and evidenced with clarity.
This level is designed for organisations handling sensitive, confidential, or regulated data where operational assurance, traceability, and compliance alignment are critical. As with all packages, the scope remains flexible and can be formally adapted, with additional services introduced where business, regulatory, or risk requirements demand greater control.
Intelligent, proactive IT operations
Every package includes direct access to senior engineers who operate as an extension of your organisation. Systems are continuously monitored, risks are identified early, and corrective action is taken before disruption occurs.
We combine operational discipline, structured monitoring, and security visibility to maintain stable, controlled, and predictable IT performance across your environment.
Speak with a senior engineer
Request a short consultation and we will assess your environment, risk profile, and operational needs. You will receive a clear recommendation, defined scope, and practical next steps aligned to your business.
IT Support Packages FAQs
Can you migrate us from another IT provider?
Yes. We manage transitions carefully to avoid disruption. If you move to one of our IT support packages Aberdeen businesses use, you will receive a clear transition plan, staged onboarding, and full visibility of what changes and when systems come under management.
What makes your IT support packages different?
Most providers sell reactive support. Our IT support packages Aberdeen organisations choose combine security, visibility, monitoring, and accountability into a structured operating model. This ensures your environment remains controlled, reviewable, and protected rather than simply supported.
Is onboarding included in the package?
Yes. All IT support packages Aberdeen clients select include structured onboarding. Monitoring, security controls, and reporting are configured properly from the start so your systems are actively protected and fully visible.
Can we upgrade or downgrade our package later?
Yes. IT support packages Aberdeen businesses rely on are designed to remain flexible. As your risk level, growth, or operational needs change, packages can be formally adjusted and additional services can be introduced where required.
Do all packages include the same level of IT support?
Yes. Every IT support package includes direct access to senior engineers, structured monitoring, and operational oversight. The difference between packages is the depth of security, reporting, and governance, not the quality of support.
Are we locked into a long-term contract?
No. IT support packages Aberdeen organisations adopt are reviewed regularly to ensure they still align with business requirements. We focus on suitability and operational value rather than locking clients into outdated scope.
What is not included by default?
Large infrastructure changes, major migrations, and one-off project work usually sit outside core managed IT support packages. If something falls outside scope, it is always confirmed clearly before any work begins.
Do you support Microsoft 365 environments?
Yes. Our IT support packages Aberdeen businesses use are designed around Microsoft 365. We manage tenant security, identity controls, device compliance, configuration standards, and audit visibility. The package level determines the depth of monitoring and governance applied.
How is pricing structured for your IT support packages?
Pricing is tailored to your environment. IT support packages Aberdeen organisations select are typically based on user count, device estate, security level, and any compliance requirements. Packages remain flexible, and additional services can be formally added as your operational needs evolve.
What level of security is included in your IT support packages?
Every package includes professionally managed security controls by default. Our IT support packages Aberdeen businesses rely on provide layered protection, monitored systems, and controlled configuration from day one. Professional establishes a strong security baseline, Advanced introduces deeper threat detection and reporting, and Enterprise provides enhanced governance and high-assurance oversight for organisations that require greater protection.
Will we receive reports on the Professional package?
Yes. All IT support packages Aberdeen organisations use include reporting and system visibility. The Professional package provides baseline auditing and operational insight, while Advanced and Enterprise extend this into deeper analysis, security reporting, and management-level review to support stronger oversight and decision-making.
Do you provide support for compliance or audits?
Yes. Our IT support packages Aberdeen regulated organisations rely on are designed to support audit and compliance requirements. We provide configuration evidence, security control reporting, and technical documentation to help demonstrate governance, traceability, and operational control when required.
Can we speak to someone before choosing a package?
Yes. Before selecting from our IT support packages Aberdeen businesses rely on, you can speak directly with a senior engineer. We assess your environment, risk exposure, and operational requirements, then recommend the most appropriate package based on technical suitability rather than sales pressure.
Our core service areas
IT services & support
Managed IT services for SMEs that need reliable support, proactive monitoring, and clear ownership of their IT environment. Choose fully managed IT or outsourced IT management for ongoing technical leadership and operational stability.
- Complete managed IT support
- Outsourced IT manager for strategic oversight
- Pay as you go IT support for flexible assistance
- Device, server, and network management
Cyber Security Services
Cyber security services for small and mid-sized businesses, including managed detection and response, email security, vulnerability scanning and staff awareness training.
- Managed detection and response (MDR/XDR)
- Email spam and phishing protection
- Vulnerability scanning and patching
- Security awareness and phishing training
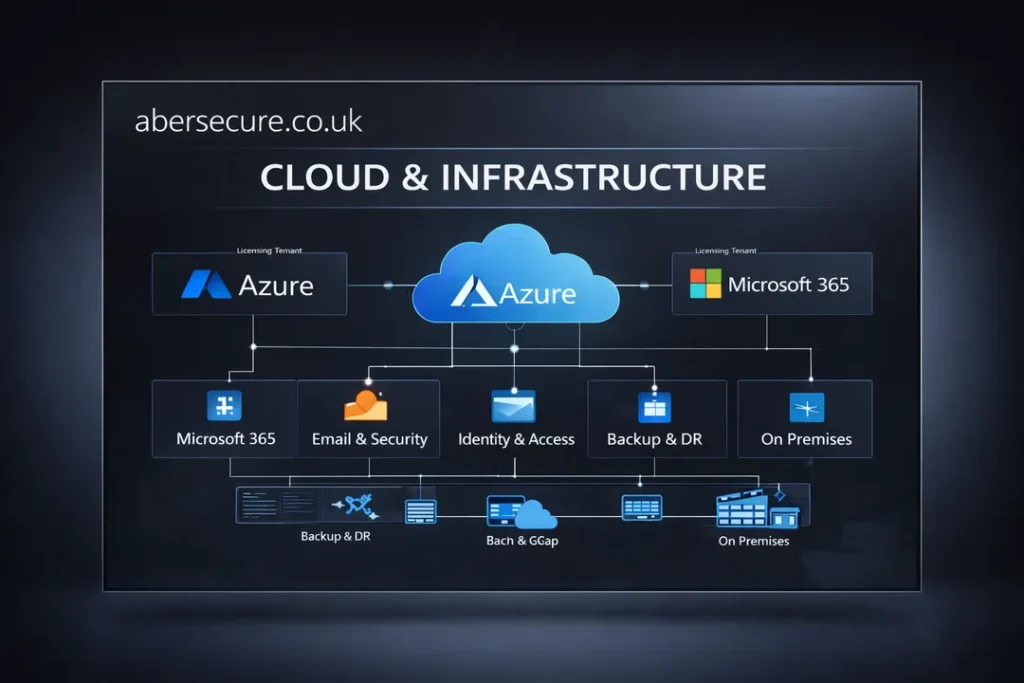
Cloud & Infrastructure
Cloud and infrastructure services covering Microsoft 365, Azure, backup and recovery, server virtualisation and secure remote access for hybrid teams.
- Microsoft 365 management and licensing
- Azure hosting and virtual servers
- Backup, disaster recovery and continuity
- Secure remote access for hybrid teams
Web & Digital Services
Web and digital services including managed hosting, website security, SEO care and domain and email branding, so your online presence stays fast, safe and professional.
- Managed website hosting and care
- Website security and uptime monitoring
- SEO care and performance optimisation
- Domain, DNS and email branding setup